PAST RESEARCH ON TRUSTWORTHY AUTONOMY
[Jump to:
Introduction |
Section 1. Resource Aware Learning and Control via Submodular Optimization |
Section 2. Denial-of-Service Robust Learning and Control via Combinatorial Optimization |
Section 3. Deception Robust Perception]
INTRODUCTION
In the future, mobile robots will be supporting our efforts in safety-critical tasks of search and rescue (e.g., localizing people in burning buildings), autonomous navigation (e.g., self-driving flying cars), and surveillance (e.g., tracking adversarial behavior). To complete the tasks, robots with heterogeneous capabilities, such as speed, sensing, and payload, will dynamically form teams, agree on navigation and other action plans, and act. The robots will rely on a collaborative distributed intelligence, communicating only with their neighbors via wireless networks. And following the current technological paradigm, the robots’ learning and control capabilities will be software-driven. Overall, the robots will form a cyber-physical network, which I henceforth call an Internet of Robotic Teams (IoRT).
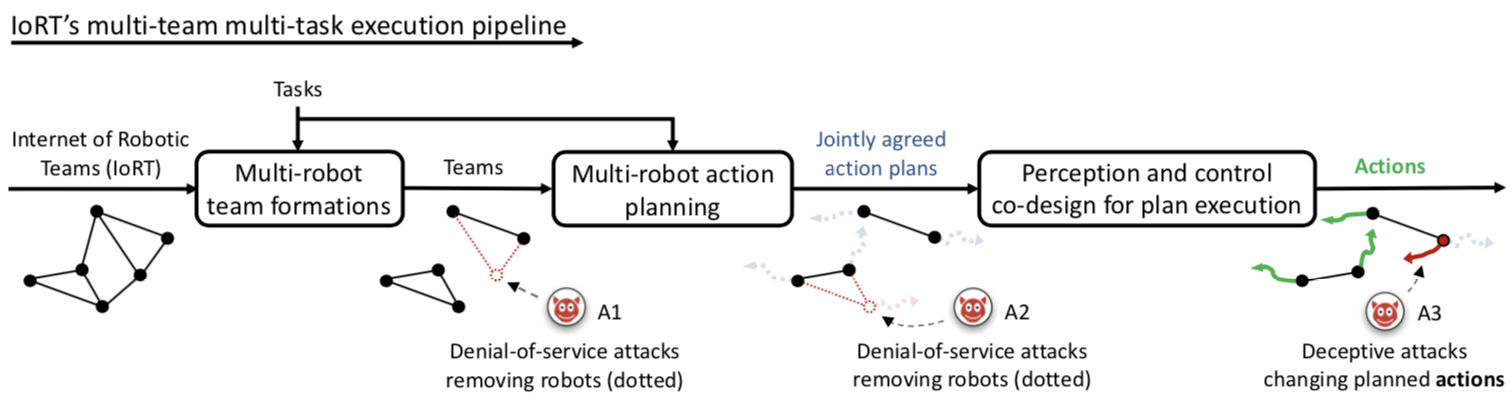
However, as any cyber-physical system, the IoRT will be vulnerable to deceptive and denial-of-service (DoS) attacks and failures that will compromise the robot teams, their plans, and their actions (cf. Fig. 2). The attacks may be physical or transduction attacks (not necessarily “cyberattacks”); and the failures may even originate from the very algorithms that aim to support autonomy (cf. Section 3 below, Deception Robust Perception). All such attacks and failures can eventually result to misinformation and robot withdrawals from the tasks, to suboptimal and untrustworthy decisions. And all lie beyond the reach of cybersecurity and classical estimation and control. Unsurprisingly, the need for a trustworthy autonomy has been listed by the National Academy of Engineering one of the grand 14 engineering challenges of the future.
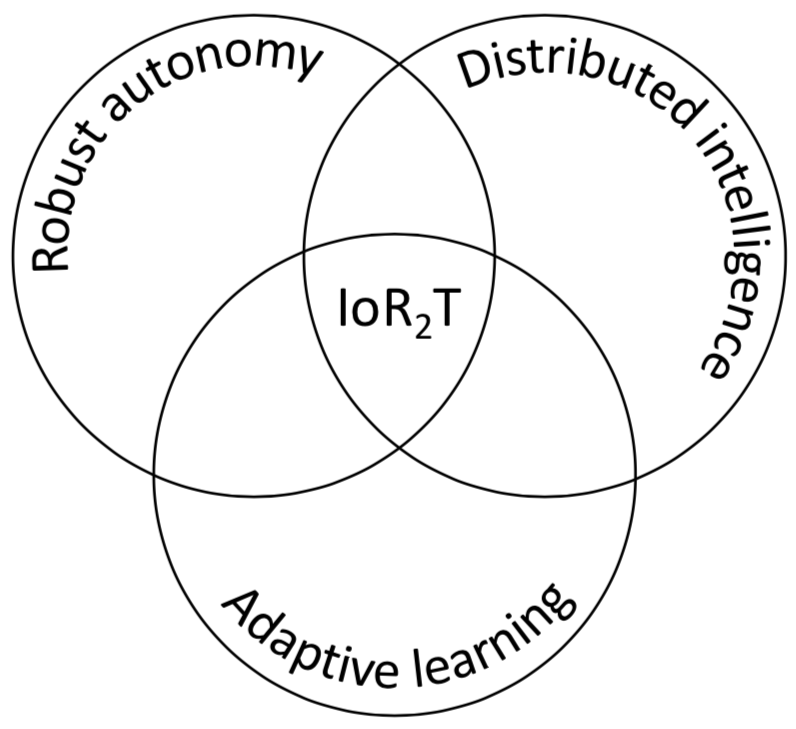
My research on trustworthy autonomy has been on enabling what I call an Internet of Resilient Robotic Teams (IoR2T), where robots will not only withstand attacks and failures, by being robust, but also will adapt and recover, by being resilient. To this end, I have worked on robotics and control towards a provably robust autonomy against deception and DoS attacks and failures (cf. Fig 2), identifying fundamental limits, and contributing provably optimal algorithms. I have demonstrated the research outcomes in applications, in tasks of autonomous navigation and multi-robot planning for exploration, search and rescue, and surveillance.
[Introduction | Section 1 | Section 2 | Section 3]
1. ReSource-aware learning and control
In a world of connected machines, from the Internet of Things (IoT) to the IoR2T, competitions for resources arise: from how to allocate the available power (when to activate what) to how to allocate the available communication and computation bandwidth (when to communicate and compute what). Hence, towards the IoR2T, a first step is to address the necessity for robotic and, more broadly, cyber-physical systems (CPS) that can successfully operate despite power, communication, and computation constraints.
The first key contribution of my PhD was to identify first fundamental limits towards resource-constrained operation of CPS in terms of their learning and control capabilities, and to develop provably near-optimal algorithms to reach the limits. To identify the limits, I employed tools of control and computational complexity theory. mTo develop the algorithms, I employed tools of combinatorial optimization, proving properties of discrete convexity, namely, of submodularity.
SELECTED PUBLICATIONS
- V. Tzoumas, L. Carlone, G. J. Pappas, A. Jadbabaie. LQG Control and Sensing Co-Design. IEEE Transactions of Automatic Control (TAC), 2021.
- A. Jadbabaie, A. Olshevsky, G. J. Pappas, V. Tzoumas. Minimal Reachability is Hard to Approximate. IEEE Transactions on Automatic Control (TAC), 2019.
- V. Tzoumas, Y. Xue, S. Pequito, P. Bogdan, G. J. Pappas. Selecting Sensors in Biological Fractional-Order Systems. IEEE Transactions on Control of Network Systems (TCNS), Vol. 5, No. 2, 2018.
- V. Tzoumas, M. A. Rahimian, G. J. Pappas, A. Jadbabaie. Minimal Actuator Placement with Bounds on Control Effort. IEEE Transactions on Control of Network Systems (TCNS), Vol. 3, No. 1, 2016.
[Introduction | Section 1 | Section 2 | Section 3]
2. Denial-of-service robust learning and control via combinatorial optimization
But the robots and CPS composing the IoT and IoR2T are vulnerable to denial-of-service (DoS) attacks and failures that can shut down subsets of the robots’ learning and control capabilities: sensors, actuators, communication channels, or even entire robots; e.g., see A1-A2 in Fig. 1. Although much research has focused against deceptive attacks and failures, little work has focused against DoS attacks and failures, and none has developed a generalized framework against any number of DoS attacks and failures.

My PhD research contributed such a general framework providing the first provably near-optimal algorithms for robust combinatorial optimization against any number of DoS attacks. The algorithms not only enabled the DoS-robustification of the resource-aware designs in Section 1. They also enabled the first DoS-robust multi-robot planning methods for navigation tasks of information gathering, such as search and rescue (e.g., localizing people in burning buildings), and surveillance (e.g., tracking adversarial behavior) —see selected publications below. The validation approach used small-scale hardware experiments (cf. figure to the right), and large-scale simulator experiments in Gazebo. The algorithms also apply to discrete optimization problems in machine learning (e.g., data summarization, feature selection).
SELECTED PUBLICATIONS
- V. Tzoumas, A. Jadbabaie, G. J. Pappas. Robust and Adaptive Sequential Submodular Optimization, IEEE Transactions on Automatic Control (TAC), in press, 2022.
- B. Schlotfeldt, V. Tzoumas, G. J. Pappas. Resilient Active Information Acquisition with Teams of Robots, IEEE Transactions on Robotics (TRO), in press, 2021.
- † L. Zhou, V. Tzoumas, G. J. Pappas, P. Tokekar, Resilient Active Target Tracking with Multiple Robots. IEEE Robotics & Automation Letters (RAL), Vol. 4, No. 1, 2019.
- B. Schlotfeldt, V. Tzoumas, D. Thakur, G. J. Pappas. Resilient Active Information Gathering with Mobile Robots. IEEE/RSJ International Conference on Intelligent Robots and Systems (IROS), 2018.
- V. Tzoumas, K. Gatsis, A. Jadbabaie, G. J. Pappas. Resilient Monotone Submodular Function Maximization (slides). IEEE Conference on Decision and Control (CDC), 2017.
Best Student Paper Award Finalist (4 finalists, out of >1,000 accepted papers)
† All theorems in this paper, as noted therein, are corollaries of the theorems proved in Resilient Non-Submodular Maximization Over Matroid Constraints, by V. Tzoumas, A. Jadbabaie, G. J. Pappas, 2018.
[Introduction | Section 1 | Section 2 | Section 3]
3. Deception robust perception
Besides DoS-robust designs and navigation plans, for an IoR2T future where robots will reliably navigate the world we also need reliable robotic navigational perception capabilities such as object recognition, scene reconstruction, and simultaneous localization and mapping (SLAM). The current algorithms supporting such capabilities are brittle to deceptive failures, namely, outliers, caused by sensor malfunctions or incorrect data associations; i.e., the outliers can be interpreted as deceptive attacks by nature (A3 in Fig. 1).
During my post-doc, my collaborators and I developed real-time outlier-robust algorithms with broad applicability to all perception problems above, employing combinatorial and non-convex optimization. The algorithms outperform the state of the art in all experimental validations, in terms of both outlier-robustness and running time. The validation approach used real-world datasets.
As such, our proposed algorithms promise to be valid replacements of the current algorithms for outlier-robust perception, including RANSAC, which is significantly slower and brittler to outliers, yet has been the standard algorithm for outlier-robust perception (and more broadly, for outlier-robust estimation in statistics, e.g., for learning and prediction) for the last 30 years.
Selected publications
- P. Antonante, V. Tzoumas, H. Yang, L. Carlone. Outlier-Robust Estimation: Hardness, Minimally-Tuned Algorithms, and Applications, IEEE Transactions on Robotics (TRO), in press, 2022.
- H. Yang, P. Antonante, V. Tzoumas, L. Carlone. Graduated Non-Convexity for Robust Spatial Perception: From Non-Minimal Solvers to Global Outlier Rejection (video presentation). IEEE Robotics & Automation Letters (RAL), 2020, and IEEE International Conference on Robotics and Automation (ICRA).
Best Paper Award in Robot Vision, ICRA 2020.
Honorable Mention, RA-L 2020. - V. Tzoumas, P. Antonante, L. Carlone. Outlier-Robust Spatial Perception: Hardness, General-Purpose Algorithms, and Guarantees. IEEE/RSJ International Conference on Intelligent Robots and Systems (IROS), 2019.
[Introduction | Section 1 | Section 2 | Section 3]